Google Drive is built for easy access, sharing, and management of files and folders for personal and business users. More than 90% of organizations store data in the cloud, and 60% rely on cloud file storage systems like Google Drive to collaborate across remote teams, internal departments, and external partners. It’s so easy to use that many users gloss over sharing permissions and other settings designed to protect business-critical data and files from leaking outside the organization. Functionality comes first for most people. Help Net Security reported in February on the reality of how everyday users interact with cloud-based tools like Google Drive:
- 73% of employees have access to data they didn’t create
- 69% can view data they didn’t contribute to
- 59% can see data from other departments
Fortunately, taking control of your organization’s Google Drive permissions is easier than ever. And not a moment too soon with the exodus of employees from the office to working from home. Cloud infrastructures like Google Drive must be secured to protect data while preserving the best user experience possible. Here are four concepts to understand about Google Drive’s sharing and permissions settings that can help save your organization from a major data loss or breach event.
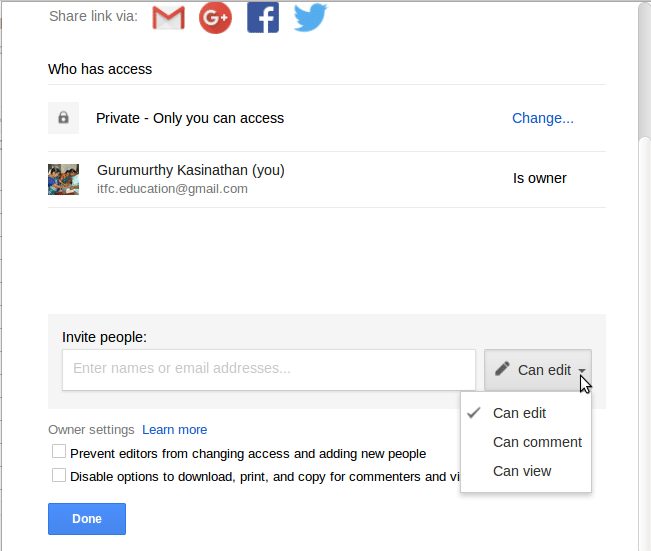
Pay close attention to your permissions settings in Google Drive (photo courtesy of Google Developers)[/caption]
#1: Know your Google Drive permissions and best practices
When sharing a document or folder with another user in Google Drive, there’s a number of ways to set access levels, both for individual users (like viewer or editor) and for an organization (like sharing only within the users within your business). It’s important to know what each of these access levels mean and how changing settings can impact the visibility — and therefore security — of your data and files.For example, Wired UK reported on a breach where the UK government accidentally revealed some of its future plans for its COVID-19 contact-tracing app by leaving them on a publicly accessible Google Drive. Wired UK found the files entitled "Product Direction: Release One" and labelled "OFFICIAL – SENSITIVE” and alerted the National Health Service. The NHS changed the permissions to private after receiving the tip.Problems like this can be avoiding by adopting the principle of least privilege, or PoLP. You probably keep a certain set of knowledge and sensitive information on a need-to-know basis within your company. PoLP is no different. As a best practice for managing applications, PoLP gives minimal access to any user or component, and only increases those privileges when explicitly instructed by an administrator.The problem here, as TechTalks points out, Google Drive and the related applications like Google Docs and Sheets tend toward a most-privilege policy. Document settings may default to private (only the user can see and make changes to the document) but it’s very easy to set a user as an editor of the document, where they can have immense control.Editors have permission to change permissions and add other users to a shared document — giving them near-administrator level powers. Google Drive permissions controls that would enforce PoLP aren’t easy to find. The option to limit the permissions of editors is hidden within the settings of the same box where you’d set the permissions level, under the gear icon at the top right of the sharing window.PoLP can reduce the chances of data leaks and breaches by limiting access to important files in Google Drive. Start thinking about who can do what with your files, and keep your data in the right hands.
Sharing settings can give users tremendous power over your org's G Drive — make sure you have visibility into how you're using these settings
#2: Control sharing settings — internally and externally
Google Drive sharing settings have a similar interface and functionality to permissions settings. There’s three choices for sharing a file for organizations: restricted, only within the group, and anyone with the link.
- Restricted means only people added by an editor can open the document or folder with this link
- Within the group means anyone in the organization's Team Drive can open the document or folder with this link
- Anyone means fully public access: anyone on the internet with the link can view
There’s an additional setting hidden behind the gear on the permissions and sharing box that’s only available to groups using Google Drive: a search setting. Clicking the box allows people in the organization or group to search for this file. This is left unchecked by default.Another less than obvious but essential setting is allowing external sharing permissions for Team Drives. The default Team Drive settings encourage sharing, which allows people outside the organization to have allowed access to files on the Team Drive. Files may be shared with non-members, and content may be downloaded, copied, or printed at will.To prevent losing important files and data, Google Team Drive's settings can be adjusted to restrict access to members-only and to disallow downloading, copying, or printing by commenters and viewers. This article from Techrepublic details how to configure these settings, by changing “full access” to “edit access” in the admin Team Drive settings panel. File owners in Google Drive can see who they’re sharing documents and folders with, by checking the users within the sharing box. But there’s currently no macro level view of which files are being shared, both where (inside or outside the Team Drive) or with whom. Until those settings arrive, stick to PoLP and double check who has access to important documents and folders to protect business-critical data from being lost or altered.
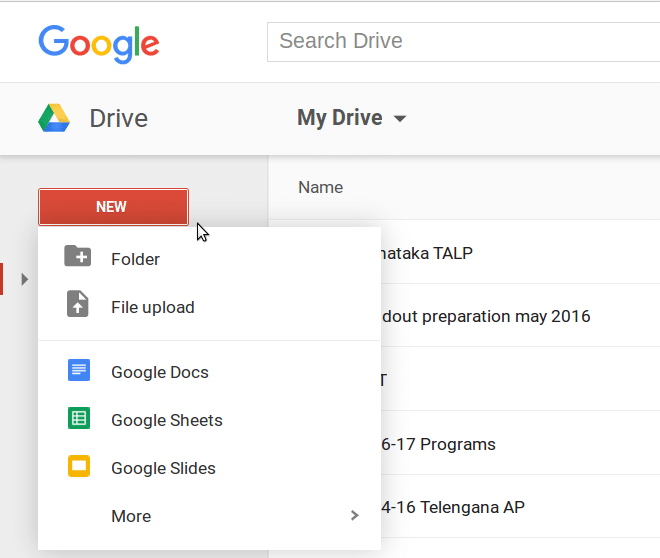
Google Drive files and folders are impacted by sharing and permissions settings (photo courtesy of Google Developers)
#3: Understand file and folder behavior in Google Drive
Permissions and sharing settings define how files and folders behave in Google Drive, especially in Team Drives. While the permissions and sharing settings are somewhat easy to find, it’s not always clear to see how these settings impact file and folder behavior.When you give access to a Google Drive folder, everything in that folder is now available at the same permission level. That means a user with edit permissions on a folder can edit, move, or copy files and folders located inside it — and even delete if your settings are configured to full access on Team Drives.From there, the same permissions extend to folders created after share access is granted. The default settings will carry through to every file and document created in the folder from there on out. In inherited permissions like this, access can't be removed from a file or folder in a shared drive. Instead these permissions must be adjusted on the direct or indirect parent from which they were inherited. Inherited permissions can be removed from items under "My Drive" or "Shared with me."Google announced that beginning Sept. 30, 2020, it will no longer be possible to place an item in multiple folders; every item will have exactly one location. This simplification of Drive's folder structure and sharing models brings some more changes to how files and folders behave, namely that moving an item will require access to share the item. Previously, only read access to the item was required.Even with the recent and upcoming changes to Drive’s sharing policies, it’s still a good idea for security leaders to retain some manual access control for sub folders and documents. A clearly defined stance on folder permissions can help prevent hidden weak points in your Google Drive security.
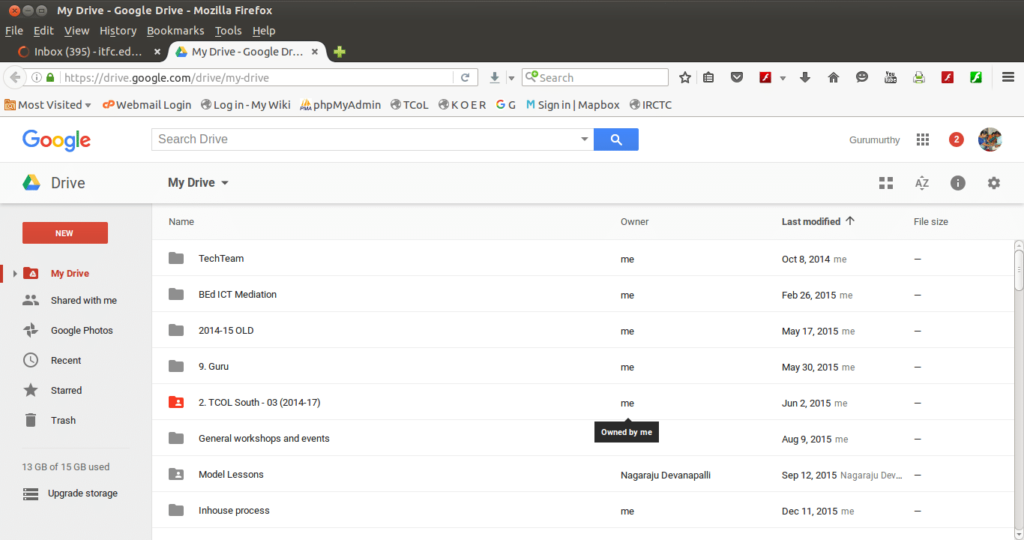
Ownership settings aren't always visible in Google Drive — but are essential for keeping your data and files safe (photo courtesy of Google Developers
#4: Establish proper ownership of files and folders
Understanding ownership of files and folders in Google Drive is just as important as knowing sharing and permissions settings. By default, the owner of a file in Google Drive is the user who created it — even in a Team Drive account. The Team Drive admin can change owner settings, but it’s still the user who owns each document, file, and folder they create in Drive.This can create a problem for organizations that don’t understand how to properly transfer ownership. One company created a new Team Drive for their organization and after moving the data over from the old Team Drive, deleted the unnecessary Drive. But since they did not change the ownership of the files and folders moved to the new Drive, they did not retain ownership in the new account. Even worse: all the company data they had in the old Drive was gone forever.A user removed from an organization’s Google Drive will make files and folders inaccessible if ownership isn’t transferred to an active user within the organization. No existing owner means no home for files to belong to. Always double check after making changes to the ownership of a folder to confirm that the files inside are transferred to the new owner.Users exiting your organization’s Team Drive can be a source of data leakage if they copy over files and folders to their personal Drives. Improper ownership settings throughout the Drive can cause headaches of losing important documents and folders permanently. Ownership and permissions oversight in Google Drive is key for protecting and retaining your data.
Find the right configurations to keep your Google Drive secure
Google Drive offers the settings you need to keep your Team Drive safe from data loss. With this post, you now have the knowledge to find the permissions settings necessary to protect important documents, data, and folders. A closer look at how your organization is sharing data and files across the Team Drive can inform future decisions for collaboration across the cloud. You can take what you’ve learned here and be a more informed cloud security practitioner with an expanded understanding of how sharing and permissions settings in Google Drive impact your data security.
About Nightfall
Nightfall is the industry’s first cloud-native DLP platform that discovers, classifies, and protects data via machine learning. Nightfall is designed to work with popular SaaS applications like Slack and Google Drive. Watch the demo video below to see Nightfall in action.


.svg)
.svg)


